The Axios Supply Chain Attack
A compromised maintainer pushed poisoned axios versions containing a cross-platform RAT.
I’m setting up cloud-based monitoring for my homelab using a Hetzner VM, and I wanted the cloud VM to be the single entry point to my infrastructure. For that I’m using Tailscale — not just client-to-site, but site-to-site so both subnets can reach each other without exposing anything publicly.
Site-to-site L3 networking connects two subnets on your Tailscale network. Each subnet needs a subnet router, but individual devices don’t need Tailscale installed. This applies to Linux subnet routers only.
This won’t work with overlapping CIDR ranges or 4via6 subnet routing.
Two private subnets with no existing connectivity between them:
pfSense runs on FreeBSD, and Tailscale’s support for it is more limited than other platforms, so there are a few rough edges.
Go to System > Package Manager > Available Packages, search for tailscale, and install it.
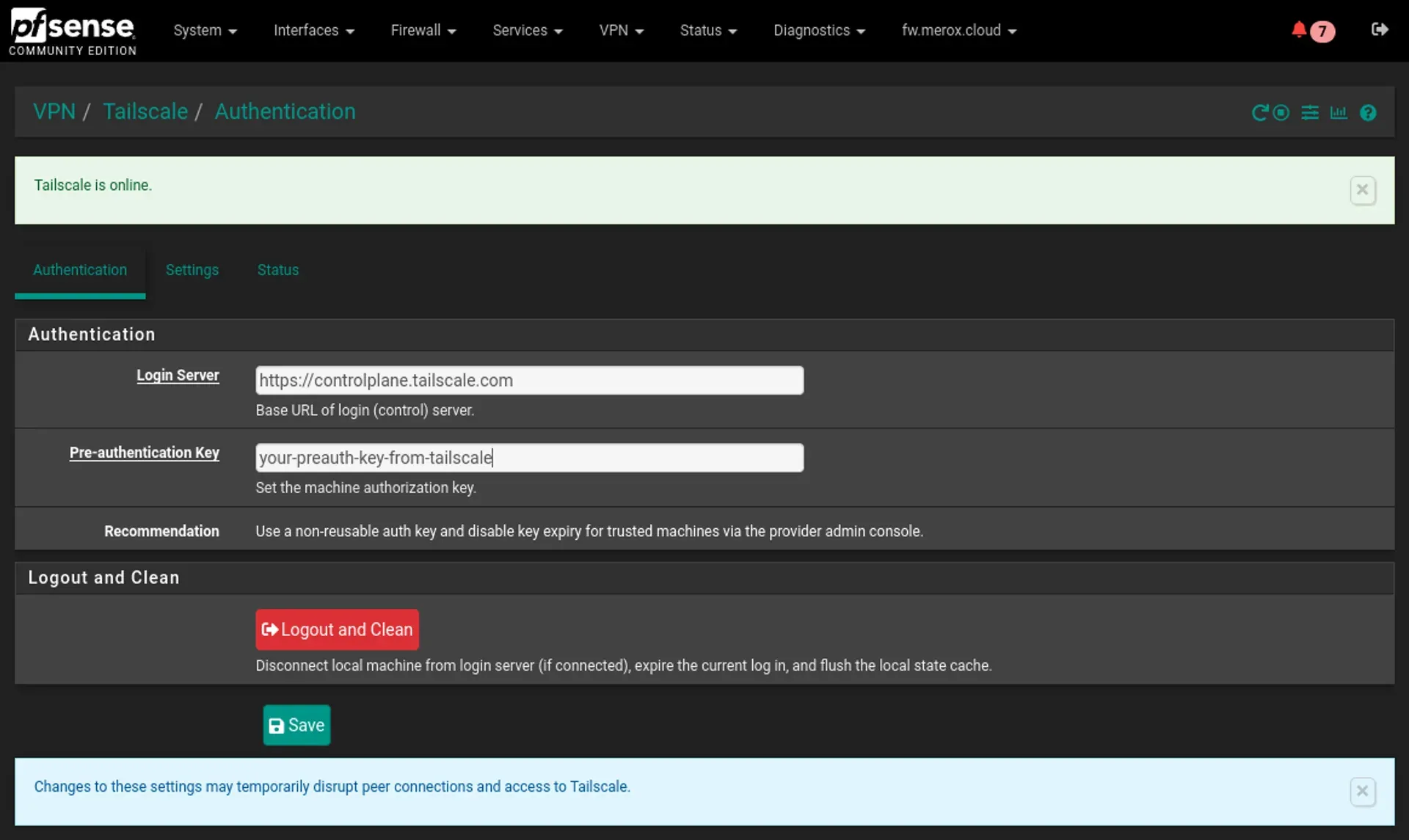
Navigate to VPN > Tailscale.
Generate an auth key at https://login.tailscale.com/admin/settings/keys and paste it in.
Settings to apply:
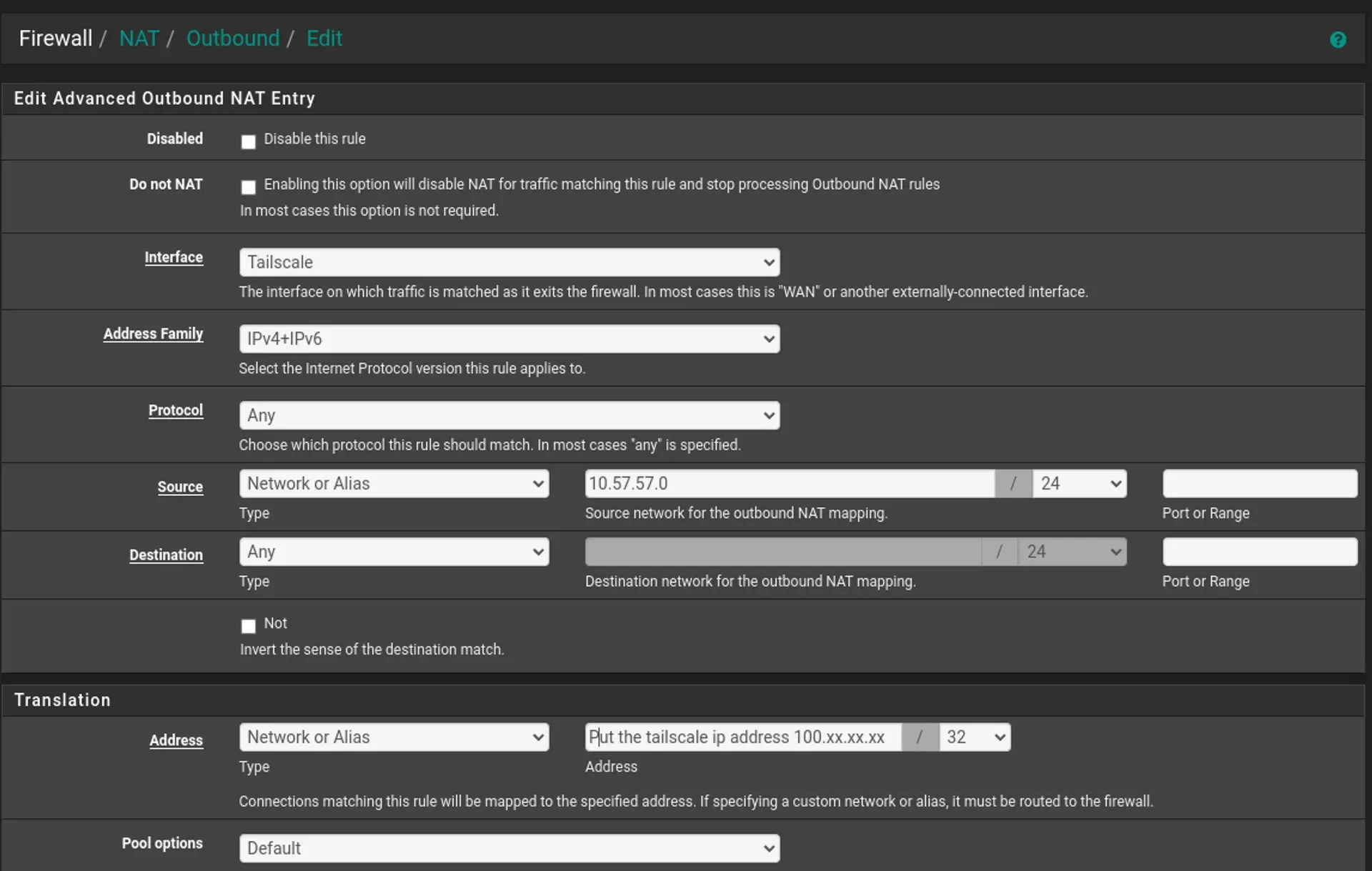
10.57.57.0/24Navigate to Firewall > NAT > Outbound and set the mode to Hybrid Outbound NAT, then create a manual mapping:
As of pfSense 23.09.1, the NAT Alias field is broken — it’s missing from the UI. Workaround: under Translation, set Address to “Network or Alias” and enter your Tailscale IP directly as 100.xx.xx.xx/32.
# Install tailscalecurl -sSL https://tailscale.com/install.sh | sh
# Activate routing for IPv4echo 'net.ipv4.ip_forward = 1' | sudo tee -a /etc/sysctl.conf
# Activate routing for IPv6echo 'net.ipv6.conf.all.forwarding = 1' | sudo tee -a /etc/sysctl.conf
# Apply routing configuration at kernel levelsudo sysctl -p /etc/sysctl.confOn the 192.168.57.254 device:
tailscale up --advertise-routes=192.168.57.0/24 --snat-subnet-routes=false --accept-routesWhat each flag does: --advertise-routes exposes the subnet to the rest of your Tailscale network. --snat-subnet-routes=false disables source NAT so the destination machine sees the actual LAN IP of the originating host rather than the subnet router — this is required for routing across multiple networks. --accept-routes tells this node to accept routes advertised by other subnet routers, including the pfSense side.
Skip this if you’re using autoApprovers.
Open the Machines page in the Tailscale admin console. Find your subnet routers (look for the Subnets badge or filter by property:subnet), click the ellipsis menu on each, select Edit route settings, and approve the advertised routes.
That’s it — the Tailscale side is done.
A compromised maintainer pushed poisoned axios versions containing a cross-platform RAT.
Practical SSH hardening for production Linux servers — key-based auth, sshd_config, 2FA, host-based auth, fail2ban, and log monitoring.
How to integrate Linux SMB file servers with Active Directory using SSSD, Samba, Kerberos, and realmd — tested on RHEL 8 and OpenSUSE 15.6.