This covers deploying Traefik as the ingress controller and wiring up cert-manager with Let’s Encrypt via Cloudflare.
Deploying Traefik
Install Helm:
curl -fsSL -o get_helm.sh https://raw.githubusercontent.com/helm/helm/main/scripts/get-helm-3chmod 700 get_helm.sh./get_helm.shkubectl create namespace traefikhelm repo add traefik https://helm.traefik.io/traefikhelm repo updategit clone https://github.com/techno-tim/launchpadIn launchpad/kubernetes/traefik-cert-manager/, open values.yaml and set the LoadBalancer IP to something from your MetalLB range, then install:
helm install --namespace=traefik traefik traefik/traefik --values=values.yamlVerify:
kubectl get svc --all-namespaces -o wideExpected output:
NAMESPACE NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE SELECTORcalico-system calico-typha ClusterIP 10.43.80.131 <none> 5473/TCP 2d20h k8s-app=calico-typhatraefik traefik LoadBalancer 10.43.185.67 10.57.57.80 80:32195/TCP,443:31598/TCP,443:31598/UDP 53s app.kubernetes.io/instance=traefik,app.kubernetes.io/name=traefikApply middleware:
kubectl apply -f default-headers.yamlkubectl get middlewareExpected output:
NAME AGEdefault-headers 4sTraefik Dashboard
Generate a base64-encoded credential:
sudo apt-get install apache2-utilshtpasswd -nb merox password | openssl base64Paste the output into dashboard/secret-dashboard.yaml:
---apiVersion: v1kind: Secretmetadata: name: traefik-dashboard-auth namespace: traefiktype: Opaquedata: users: abc123==Point your DNS server to the MetalLB IP from values.yaml:
![]()
Set your domain in dashboard/ingress.yaml:
routes: - match: Host(`traefik.k3s.your.domain`)Apply everything from the traefik/dashboard folder:
kubectl apply -f secret-dashboard.yamlkubectl get secrets --namespace traefikkubectl apply -f middleware.yamlkubectl apply -f ingress.yamlThe dashboard will be up but using a self-signed cert. The next section fixes that.
Cert-Manager
From traefik-cert-manager/cert-manager:
helm repo add jetstack https://charts.jetstack.iohelm repo updatekubectl create namespace cert-managerNote
Check the releases page and use the latest version of cert-manager.
kubectl apply -f https://github.com/cert-manager/cert-manager/releases/download/v1.17.0/cert-manager.crds.yamlhelm install cert-manager jetstack/cert-manager --namespace cert-manager --values=values.yaml --version v1.17.0Apply your Cloudflare API secret (use an API Token, not a global key):
kubectl apply -f issuers/secret-cf-token.yamlBefore applying the remaining files, edit:
issuers/letsencrypt-production.yaml:email,dnsZonescertificates/production/your-domain-com.yaml:name,secretName,commonName,dnsNames
kubectl apply -f values.yamlkubectl apply -f issuers/letsencrypt-production.yamlkubectl apply -f certificates/production/your-domain-com.yamlMonitor progress:
kubectl logs -n cert-manager -f cert-manager-(your-instance-name)kubectl get challenges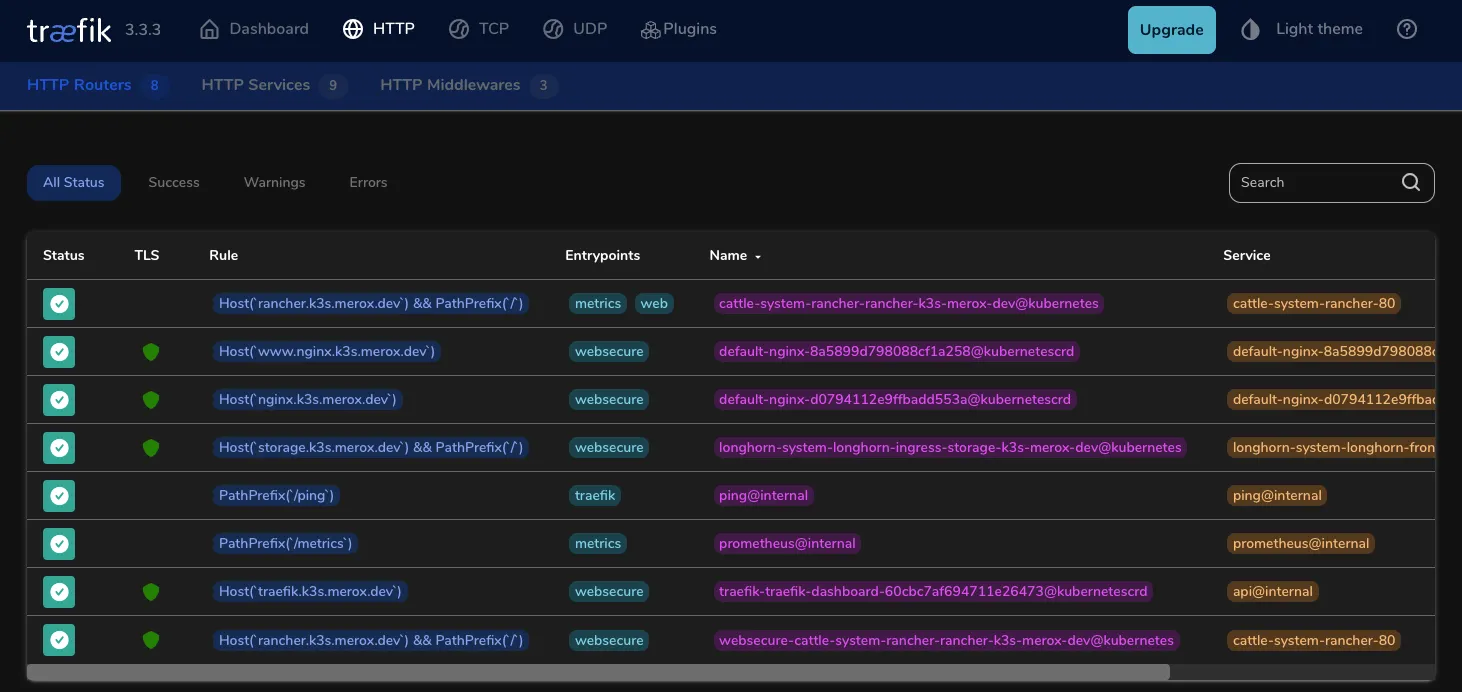
Next Steps
Proceed to the Cluster Management guide.