This covers deploying Rancher for cluster management and Longhorn for distributed persistent storage.
Rancher
helm repo add rancher-latest https://releases.rancher.com/server-charts/stablekubectl create namespace cattle-systemTraefik is already handling ingress, so set tls=external:
helm install rancher rancher-stable/rancher \ --namespace cattle-system \ --set hostname=rancher.k3s.your.domain \ --set tls=external \ --set replicas=3Create ingress.yml:
apiVersion: traefik.io/v1alpha1kind: IngressRoutemetadata: name: rancher namespace: cattle-systemspec: entryPoints: - websecure routes: - match: Host(`rancher.k3s.your.domain`) kind: Rule services: - name: rancher port: 443 middlewares: - name: default-headers tls: secretName: k3s-your-domain-tlskubectl apply -f ingress.yml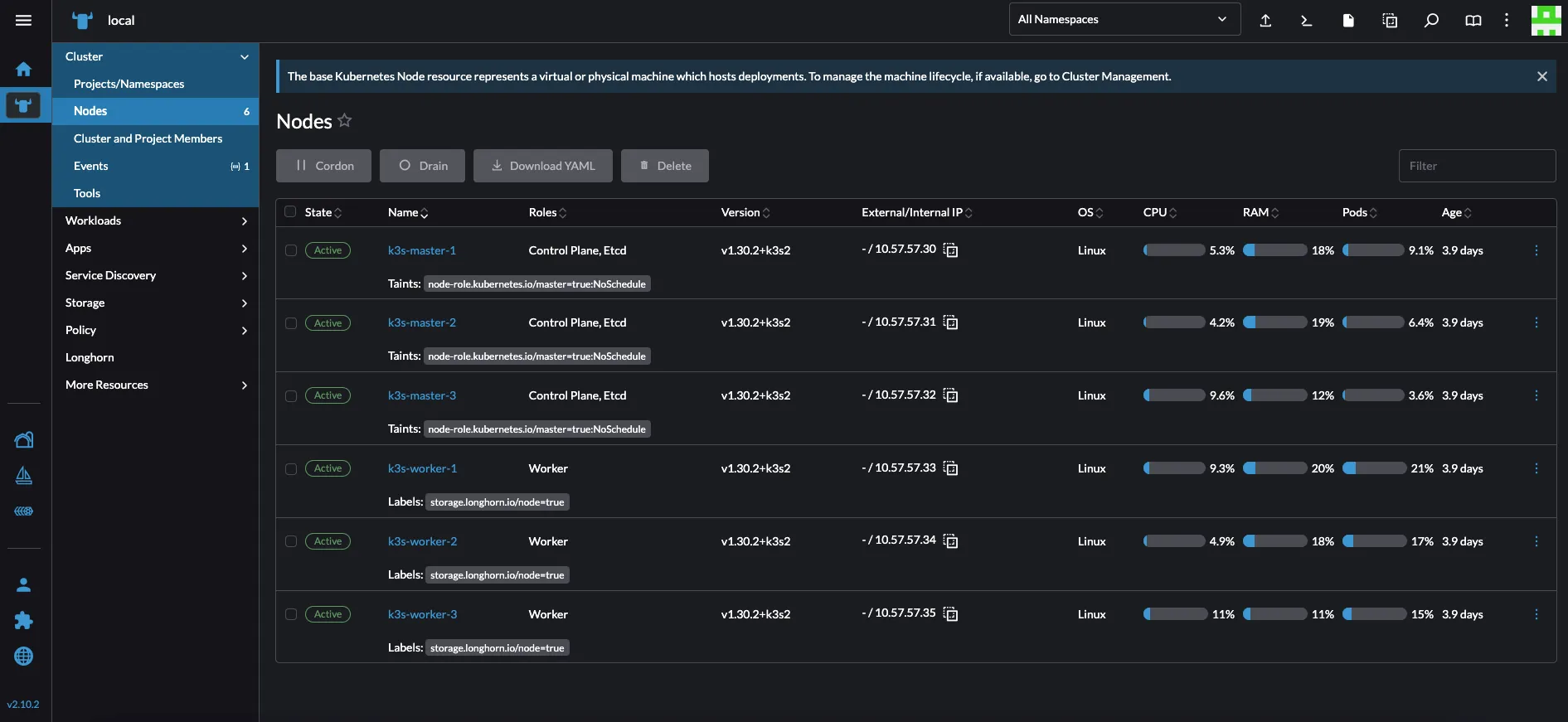
Longhorn
Install prerequisites on the nodes you want to use for storage:
sudo apt update && sudo apt install -y open-iscsi nfs-commonsudo systemctl enable iscsidsudo systemctl start iscsidLabel your three worker nodes for HA:
kubectl label node k3s-worker-1 storage.longhorn.io/node=truekubectl label node k3s-worker-2 storage.longhorn.io/node=truekubectl label node k3s-worker-3 storage.longhorn.io/node=trueDeploy (this manifest is patched to use the storage.longhorn.io/node=true label):
kubectl apply -f https://raw.githubusercontent.com/meroxdotdev/merox.docs/refs/heads/master/K3S/cluster-deployment/longhorn.yamlVerify:
kubectl get pods --namespace longhorn-system --watchkubectl get nodeskubectl get svc -n longhorn-systemExposing Longhorn via Traefik
Create middleware.yml:
apiVersion: traefik.io/v1alpha1kind: Middlewaremetadata: name: longhorn-headers namespace: longhorn-systemspec: headers: customRequestHeaders: X-Forwarded-Proto: "https"Create ingress.yml:
apiVersion: networking.k8s.io/v1kind: Ingressmetadata: name: longhorn-ingress namespace: longhorn-system annotations: traefik.ingress.kubernetes.io/router.entrypoints: websecure traefik.ingress.kubernetes.io/router.tls: "true" traefik.ingress.kubernetes.io/router.middlewares: longhorn-system-longhorn-headers@kubernetescrdspec: rules: - host: storage.k3s.your.domain http: paths: - path: / pathType: Prefix backend: service: name: longhorn-frontend port: number: 80 tls: - hosts: - storage.k3s.your.domain secretName: k3s-your-domain-tls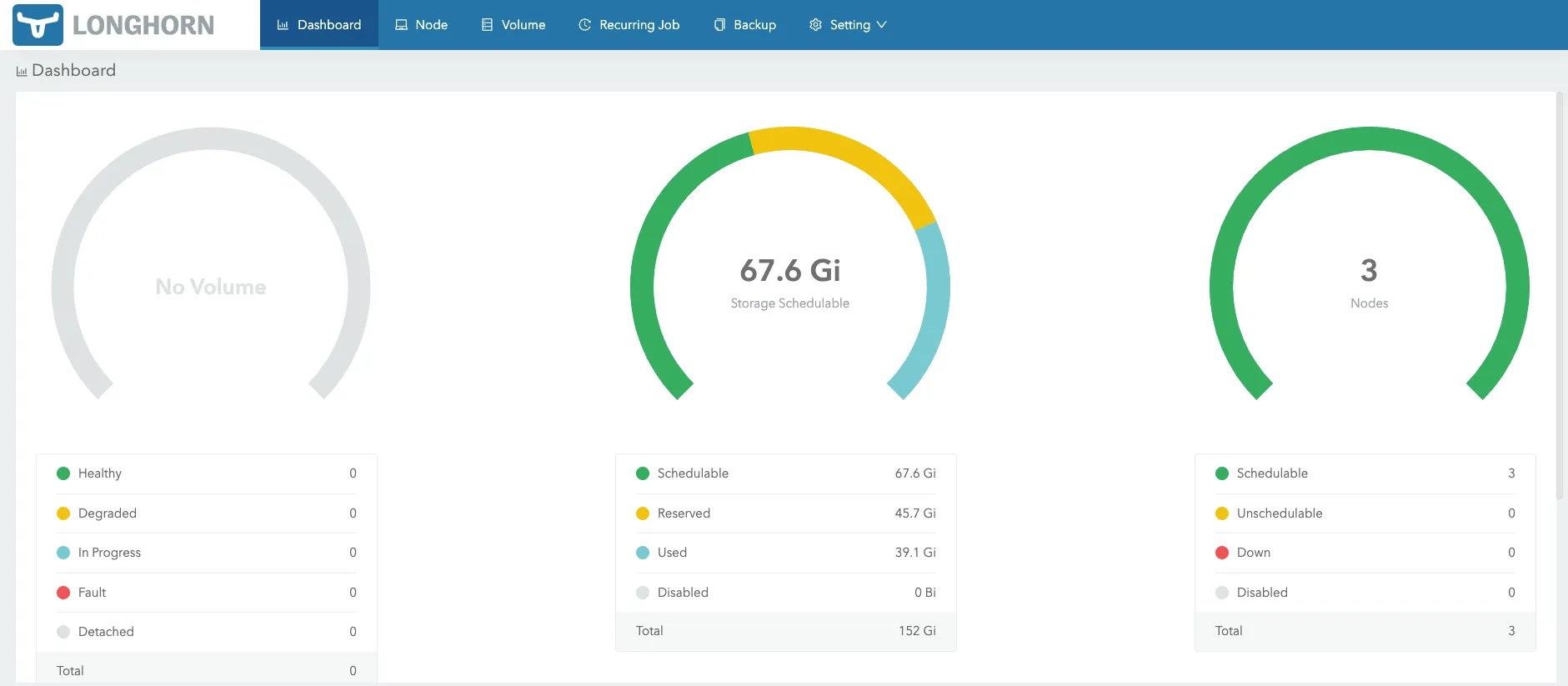
Next Steps
Proceed to the Advanced Resources guide.